HTML-Injection-Schwachstelle im Vaultwarden Admin-Dashboard
Vertrauen Sie auf eine sichere Verwaltung Ihrer Zugangsdaten? Admin-Dashboards stehen im Fokus vieler Angriffe, da sie zentralen Zugriff auf wichtige Benutzer- und Organisationsdaten bieten. Im Auftrag des Bundesamts für Sicherheit in der Informationstechnik (BSI) haben wir Vaultwarden gezielt mit statischer Codeanalyse und Penetrationstests überprüft. Dabei ist uns eine kritische HTML-Injection-Sicherheitslücke im Admin-Dashboard bis einschließlich Version 1.30.3 aufgefallen.
Angreifer konnten speziell gestaltete HTML-Inhalte in die Felder „Organisation“ und „Benutzer“ injizieren. Diese wurden im Admin-Dashboard falsch dargestellt und können unter Umständen dazu verwendet werden, Administratoren auf manipulierte Webseiten weiterzuleiten oder das Erscheinungsbild des Dashboards zu verfälschen. Zwar verhindert die strenge Content-Security-Policy von Vaultwarden JavaScript-Angriffe wirkungsvoll, dennoch bleiben Ausnutzungsmöglichkeiten bestehen, wie etwa unerwünschte Weiterleitungen.
Wir haben die Schwachstelle umgehend gemeldet und die Entwickler haben in Version 1.32.0 eine Lösung bereitgestellt.
In diesem Beitrag erfahren Sie, wie die Sicherheitslücke zustande kam, welche Risiken für Ihr Unternehmen bestehen und wie Sie sich wirkungsvoll schützen können. Nutzen Sie unsere unabhängige Expertise. Wir beraten Sie gerne rund um Ihre IT-Sicherheit und unterstützen Sie dabei, Ihre Systeme immer auf dem neuesten Stand zu halten.
In Vaultwarden Version 1.30.3 (oder früher) wurde eine HTML-Injection-Sicherheitslücke entdeckt. Wir haben diese Sicherheitslücke dem Entwickler gemeldet, der das Problem behoben und die Sicherheitslücke in Version 1.32.0 geschlossen hat.
Beschreibung
Vaultwarden wird mit einem Admin-Dashboard ausgeliefert. Diese Funktion kann gemäß den hier beschriebenen Anweisungen aktiviert werden: https://github.com/dani-garcia/vaultwarden/wiki/Enabling-admin-page
Nach der Aktivierung ist das Vaultwarden-Admin-Dashboard unter /admin verfügbar. Das Vaultwarden-Admin-Dashboard verfügt über eine Seite für die Benutzerverwaltung. Für Benutzer, die Mitglieder einer Organisation sind, kann der Administrator die Rollenzuweisung über einen modalen Dialog schnell ändern.
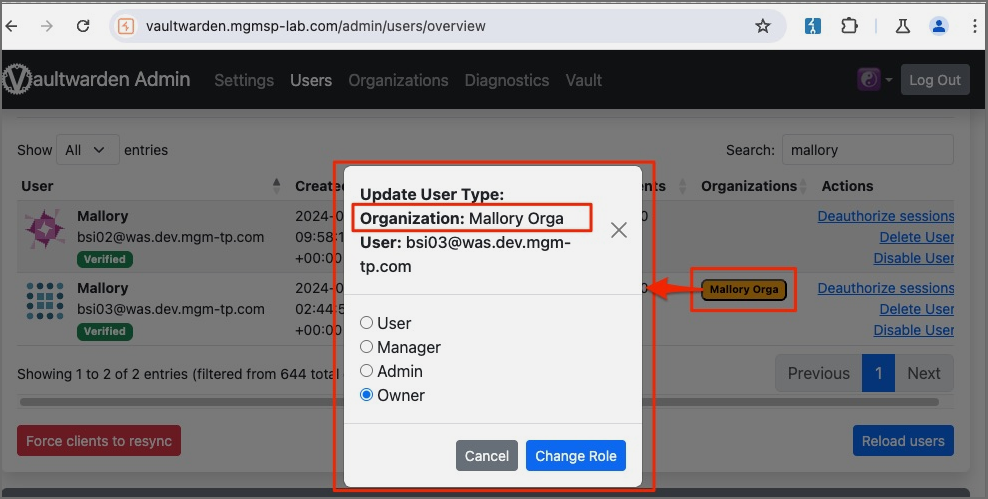
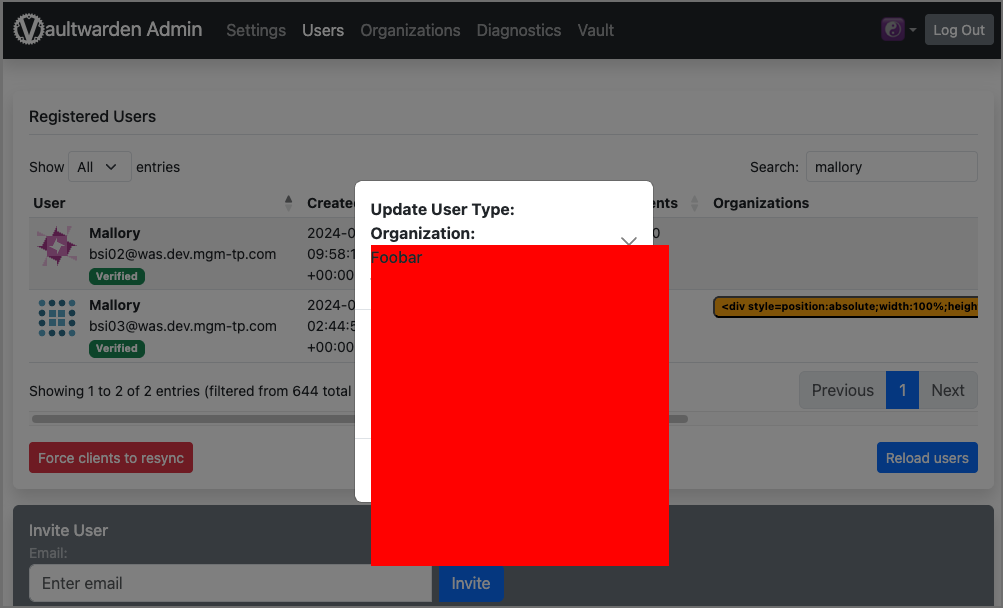
Dieser modale Dialog ist anfällig für HTML-Injektionen. Payloads können in die Felder „Organisation” und „Benutzer” injiziert werden. Um das Problem zu demonstrieren, wurde die folgende Payload im Feld „Organisation” gespeichert.
<div style=position:absolute;width:100%;height:100%;background:red;z-index:9>Foobar</div>
Die injizierte Payload wurde als HTML-Code geparst und auf der anfälligen Seite gerendert:
Beachten Sie, dass Vaultwarden standardmäßig eine sehr strenge Content-Security-Policy (CSP) verwendet. Diese CSP verhindert erfolgreich Versuche, JavaScript über den injizierten HTML-Code auszuführen.
content-security-policy:
default-src ‚self‘;
base-uri ‚self‘;
form-action ‚self‘;
object-src ‚self‘ blob:;
script-src ‚self‘ 'wasm-unsafe-eval';
style-src ‚self‘ 'unsafe-inline';
child-src ‚self‘ https://*.duosecurity.com https://*.duofederal.com;
frame-src ‚self‘ https://*.duosecurity.com https://*.duofederal.com;
frame-ancestors ‚self‘ chrome-extension://nngceckbapebfimnlniiiahkandclblb chrome-extension://jbkfoedolllekgbhcbcoahefnbanhhlh moz-extension://* ;
img-src ‚self‘ data: https://haveibeenpwned.com ;
connect-src ‚self‘ https://api.pwnedpasswords.com https://api.2fa.directory https://app.simplelogin.io/api/ https://app.addy.io/api/ https://api.fastmail.com/ https://api.forwardemail.net ;Eine gewisse Ausnutzbarkeit ist dennoch möglich. Beispielsweise könnte die folgende Payload verwendet werden, um betroffene Benutzer beim Aufruf des Dialogs auf beliebige andere Seiten umzuleiten.
<meta name=language content=1;https://www.mgm-sp.com HTTP-EQUIV=refresh />
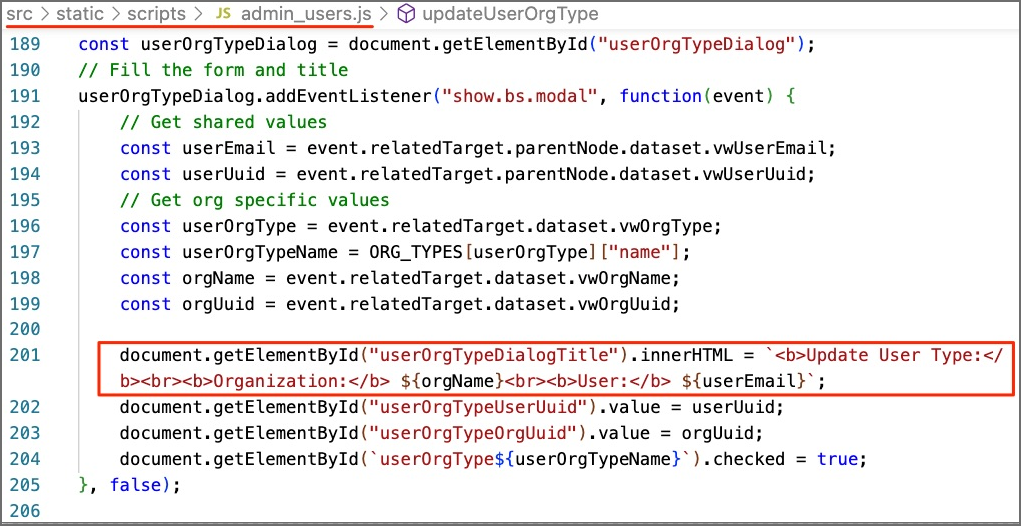
Der anfällige Quellcode ist hier zu finden: https://github.com/dani-garcia/vaultwarden/blob/1.30.3/src/static/scripts/admin_users.js#L201
Zugewiesene CVE: https://nvd.nist.gov/vuln/detail/CVE-2024-39926
Betroffene Komponente: https://github.com/dani-garcia/vaultwarden/
Angriffstyp: Remote
Auswirkung Codeausführung: Ja
Angriffsvektoren: Um die Schwachstelle auszunutzen, muss der Benutzer auf einen vom Angreifer vorbereiteten bösartigen Link klicken.
Referenz:
https://github.com/dani-garcia/vaultwarden/pull/4737
https://github.com/dani-garcia/vaultwarden/releases/tag/1.32.0

